-
Featured services
2026 Global AI Report: A Playbook for AI Leaders
Why AI strategy is your business strategy: The acceleration toward an AI-native state. Explore executive insights from AI leaders.
Access the playbook -
Services
View all services and productsLeverage our capabilities to accelerate your business transformation.
-
Services
Enterprise Networking
-
Services
Cloud
-
Services
Consulting
-
-
Services
Data and Analytics
-
Services
Infrastructure Solutions
-
Services
Global Data Centers
-
Services
CX and Digital Products
-
Services
Application Services
-
Services
Sustainability Services
-
Services
Digital Workplace
-
Services
Business Process Services
-
Services
Generative AI
-
Services
Cybersecurity
-
Services
Enterprise Application Platforms
![]()
Accelerate outcomes with agentic AI
Optimize workflows and get results with NTT DATA's Smart AI AgentTM Ecosystem
Create your roadmap -
-
-
Insights
Insights
Recent Insights
-
The Future of Networking in 2025 and Beyond
-
Using the cloud to cut costs needs the right approach
When organizations focus on transformation, a move to the cloud can deliver cost savings – but they often need expert advice to help them along their journey
-
Make zero trust security work for your organization
Make zero trust security work for your organization across hybrid work environments.
-
-
![]()
2026 Global AI Report: A Playbook for AI Leaders
Why AI strategy is your business strategy: The acceleration toward an AI-native state. Explore executive insights from AI leaders.
Access the playbook -
-
Discover how we accelerate your business transformation
-
About us
CLIENT STORIES
-
Liantis
Over time, Liantis – an established HR company in Belgium – had built up data islands and isolated solutions as part of their legacy system.
-
Randstad
We ensured that Randstad’s migration to Genesys Cloud CX had no impact on availability, ensuring an exceptional user experience for clients and talent.
-
-
CLIENT STORIES
-
Liantis
Over time, Liantis – an established HR company in Belgium – had built up data islands and isolated solutions as part of their legacy system.
-
Randstad
We ensured that Randstad’s migration to Genesys Cloud CX had no impact on availability, ensuring an exceptional user experience for clients and talent.
-
![]()
2026 Global AI Report: A Playbook for AI Leaders
Why AI strategy is your business strategy: The acceleration toward an AI-native state. Explore executive insights from AI leaders.
Access the playbook -
- Careers
Topics in this article
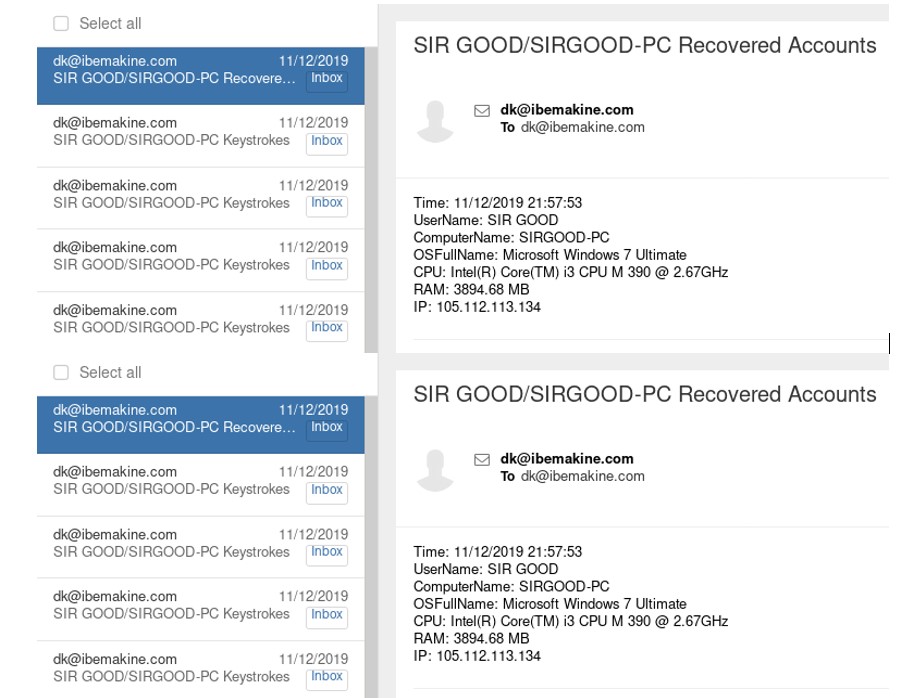
Jacob Faires, Senior Threat Research Analyst, NTT The Global Threat Intelligence Team (GTIC) monitors active malware campaigns all over the world. The Obasi campaign, named after one of the threat actors, is an active campaign we are currently tracking. This campaign led us to a new Agent Tesla sample that pivoted to a new mailbox not currently being used by any of the other actors of the Obasi campaign.
bk@ibekamine[.]com
The bk@ email is being used for exfiltration by Agent Tesla malware samples. Originally, GTIC thought the address was being managed by the threat actor Zeel Ken Obasi. Further research showed it was a different individual from the same region.
It is common practice for threat actors to send test emails to test the functionality of malware samples. The initial Agent Tesla test email was from a UK IP address (31.3.251.197). After the initial test email, all following IPs point to Lagos, Nigeria as the location of the actor.
105.112.112.57
105.112.112.78
105.112.112.103
105.112.112.195
105.112.113.12
105.112.113.92
105.112.113.134
105.112.114.55
105.112.114.117
105.112.114.201
105.112.120.27
105.112.121.167
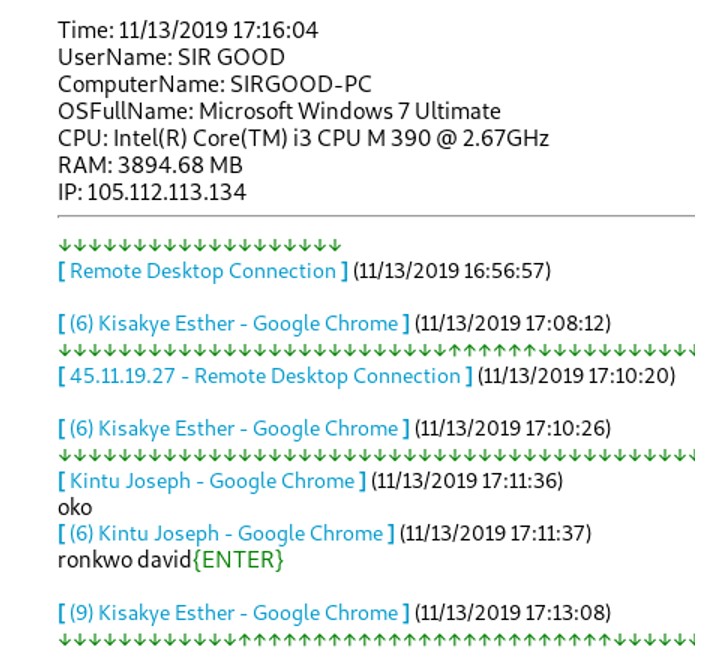
Other logs showed similarities to the Obasi campaign:
- Typo squatting and spear phishing
- DNS hosting providers
- Delivery of Agent Tesla
- SMTP exfiltration traffic over port 587 without TLS
- This includes login information. SMTP and IMAP credentials were in clear text.
- Auto forwarding logs
- Unlike Obasi’s campaigns, these logs are primarily forwarded to a Yandex account instead of a mail.ru account.
Operational security (OPSec)
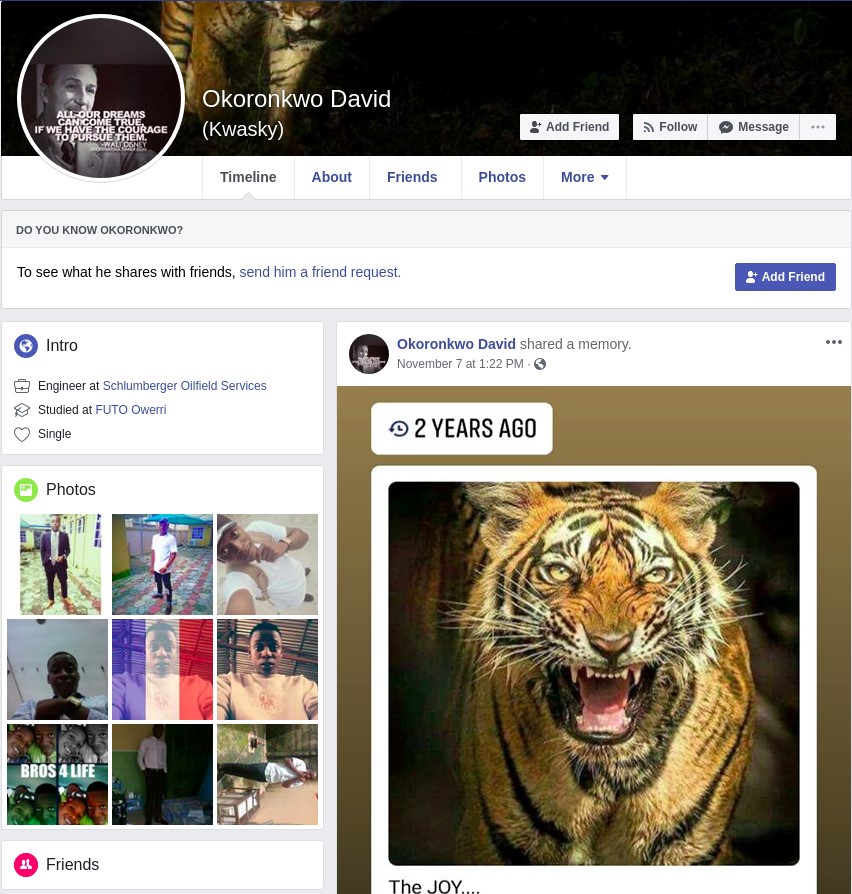
As in the case of Obasi, the actor ran their keylogger malware on themselves. Logs containing information about the actor's machine were found in the mail account. Following the compromised actor’s actions showed them adding a friend, Okoronkwo David, to compromised Facebook accounts.
This led to the Facebook profile for Okoronkwo David.
https://www.facebook.com/kwasky
While it’s possible that this account is fake and managed by the threat actor as a fake persona, the possibility is very low. Other indicators in the campaign show extremely low levels of OPSec, and security in general, practiced by the actor. Passwords are variations on the actor's name and the Agent Tesla sample pre-FUD has the filename kwasky.exe, which is the nickname ascribed to the Facebook page.
IOCs
IPs
31.3.251.197
105.112.112.57
105.112.112.78
105.112.112.103
105.112.112.195
105.112.113.12
105.112.113.92
105.112.113.134
105.112.114.55
105.112.114.117
105.112.114.201
105.112.120.27
105.112.121.167
Domains
smtp.ibemakine.com
Email Addresses
SHA-256
c2c1eaf0012413da59fcce9dbf7eea9b72ab45dbb3d17429fe988158a2e5783d
d263aec0a4d338110aaae8c8ed928d7ef52e87a2fecda08663e4600f57c2a4b7
3999d4d2a2422a55d8c2b0abe9dea38443e42a21dc959d69d2c927cb2ae82db4
6fa5c0456337d4d86aeb7831f6396a8da488dab75fa6cc658c2b4f80cc379465
01da3d69232d85e63cf4a972c62271ba6163af065c146541570b62decb963ab0
19fab115271f6e556f2914eb3cdc32311d886bee1b15f0d151ae72211de31228